DNS Block Lists: Do They Actually Protect Your Privacy?
DNS block lists can reduce tracking and block malicious domains, but they’re not a complete privacy solution. Here’s what they actually protect, what they miss, and how to use them effectively in 2026.

DNS block lists can significantly reduce tracking and malicious connections by stopping requests before they reach known bad domains. But they are not a complete privacy solution and relying on them alone can create a false sense of security.
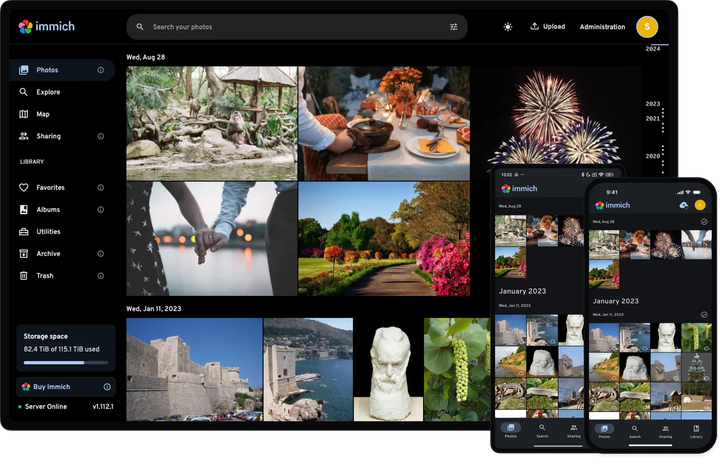
DNS-based filtering has quietly become one of the most popular “set it and forget it” tools in privacy circles. With the rise of Pi-hole, AdGuard, and router-level filtering, more people are turning to DNS block lists as a first line of defense. But in 2026, the landscape has shifted: trackers are more dynamic, apps bypass DNS, and many block lists are outdated or overly aggressive. Understanding what these lists actually do and where they fall short is essential if you care about real privacy.
Prefer listening? Click play below, or listen to this episode on RedCircle.
What are DNS block lists and how do they work?
DNS block lists are curated collections of domains associated with ads, trackers, malware, or phishing. When your device tries to resolve a domain name, the DNS system checks the block list and either blocks or redirects the request.
In practice, this means:
- Ads don’t load
- Known trackers fail to connect
- Malicious domains are cut off before they respond
Tools like Pi-hole and AdGuard rely heavily on these lists. The effectiveness of your setup is only as good as the lists you choose.
Some of the most widely used lists today are hosted on GitHub, including:
- https://github.com/hagezi/dns-blocklists
- https://github.com/blocklistproject/Lists
- https://github.com/justdomains/blocklists
These repositories are actively maintained and widely referenced in privacy communities.
Which DNS block lists are actually worth using?
Not all block lists are created equal. Some are aggressively maintained with clear policies, while others are abandoned or overly broad.
1. HaGeZi DNS Blocklists
https://github.com/hagezi/dns-blocklists
- Curated tiers (light → aggressive)
- Strong focus on minimizing false positives
- Frequently updated
Opinion: This is currently one of the best “default” choices. It balances coverage with usability better than most alternatives.
2. The Block List Project
https://github.com/blocklistproject/Lists
- Category-based lists (ads, malware, phishing, etc.)
- Modular and flexible
- Good for advanced users
Tradeoff: More control means more complexity. Most users over-stack lists and break things.
3. JustDomains Blocklists
https://github.com/justdomains/blocklists
- Clean domain-only format
- Compatible with almost everything
- Lightweight
Limitation: You lose advanced filtering rules this is simplicity over sophistication.
Protect your digital life. Subscribe for trusted privacy and security insights.
Are DNS block lists enough to protect your privacy?
No, and this is where most advice online is outdated.
DNS block lists operate at a very specific layer: domain resolution. Modern tracking increasingly happens outside that layer.
Here’s what they do not stop:
- First-party tracking (e.g., analytics from the site you visit)
- Hardcoded IP connections in apps
- Encrypted DNS bypass (DoH inside apps)
- Browser fingerprinting
- Logged DNS queries from your provider
Mozilla explains how encrypted DNS changes the threat model, but doesn’t eliminate tracking:
https://support.mozilla.org/en-US/kb/firefox-dns-over-https
Bottom line: DNS block lists reduce noise and risk, but they don’t make you anonymous or invisible.
How should you actually use DNS block lists in 2026?
This is where most setups go wrong. People stack dozens of lists, assume more is better, and end up with broken services and minimal added protection.
A better approach:
Step-by-step setup strategy
- Start with one high-quality curated list (e.g., HaGeZi “normal” tier)
- Add one specialized list (e.g., malware-only from Block List Project)
- Test your setup for breakage across:
- Banking apps
- Streaming services
- Smart home devices
- Monitor logs for blocked domains you actually need
- Only then consider adding more lists
This approach prioritizes signal over noise.

Subscribe: Spotify, YouTube, Amazon Music, RSS, Apple Podcasts
Which tools use DNS block lists and what are the tradeoffs?
DNS block lists don’t operate alone they’re implemented through tools and services. Each comes with its own privacy implications.
| Tool / Service | Type | Key Tradeoff |
|---|---|---|
| Pi-hole | Self-hosted | Full control, but requires maintenance |
| AdGuard DNS | Cloud DNS | Easy, but involves trusting a provider |
| NextDNS | Hybrid | Powerful, but logs may exist depending on settings |
Pi-hole
- Runs locally on your network
- Uses community block lists
- No third-party DNS logging by default
Privacy advantage: You control everything.
Risk: Misconfiguration and lack of updates.
AdGuard DNS
- Managed DNS filtering service
- Easy to deploy across devices
Privacy concern: You’re trusting a third party with your DNS traffic.
AdGuard publishes transparency info, but trust is still required.
NextDNS
- Highly customizable filtering
- Detailed analytics and logs
Tradeoff: Logging is optional but many users enable it, which introduces risk.
See their documentation: https://help.nextdns.io
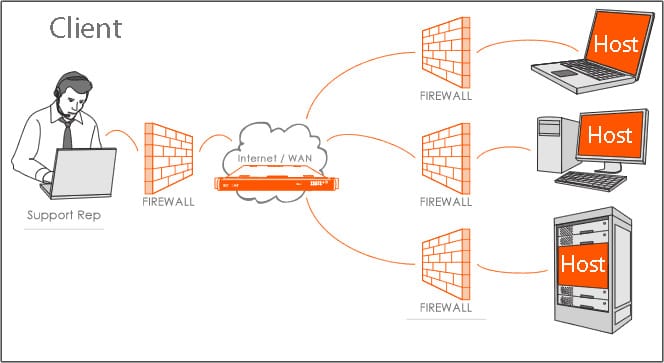
How do DNS block lists fit into a real privacy strategy?
Think of DNS filtering as layer one, not the full system.
A realistic privacy stack includes:
- DNS filtering (block lists)
- Browser-level protections (uBlock Origin, hardened settings)
- Network encryption (DoH/DoT or VPN)
- App-level awareness (many apps bypass DNS entirely)
Cloudflare’s overview of DNS security highlights how DNS is just one part of a broader system:
https://www.cloudflare.com/learning/dns/what-is-dns/
Insight: DNS block lists are best at reducing background noise, not preventing targeted tracking.
FAQs
Do DNS block lists slow down internet speed?
Usually no. In many cases, they speed things up by blocking unnecessary requests.
Can apps bypass DNS block lists?
Yes. Many apps use hardcoded IPs or encrypted DNS.
Are DNS block lists legal?
Yes. They simply prevent connections to domains you’re not modifying content.
How often should block lists be updated?
At least weekly. Good lists update automatically.
Do DNS block lists stop malware?
They can block known malicious domains, but they are not a full antivirus solution.
What should you do next?
Set up a single high-quality DNS block list today and test it critically instead of assuming it’s protecting you.